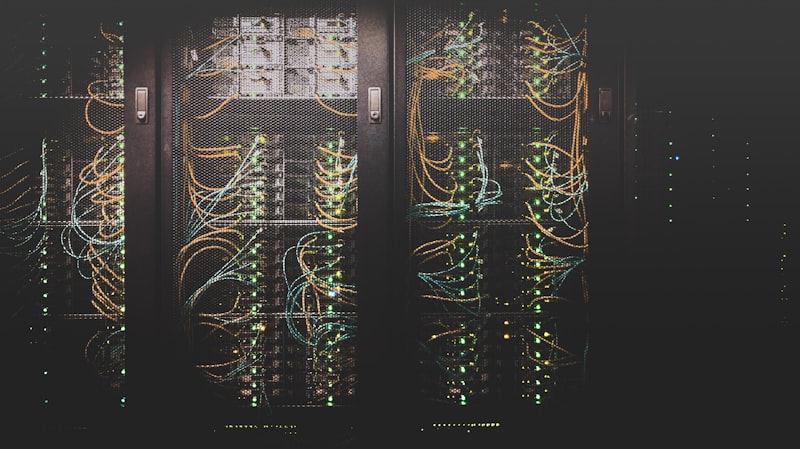
Defense in Depth
A single firewall is not enough. We build layered security architectures that protect your business from every angle.
Our Methodology
From assessment to ongoing defense — four phases to a hardened network.
Vulnerability Assessment
We scan your current network to map every device, open port, and misconfiguration — then deliver a prioritized risk report.
Architecture Design
We design a secure topology with VLAN segmentation, firewall zones, wireless coverage maps, and failover paths.
Deployment & Hardening
We install and configure firewalls, switches, and access points — then lock down every device to CIS benchmarks.
Monitoring & Tuning
Ongoing log analysis, rule optimization, firmware updates, and quarterly penetration tests to keep defenses sharp.
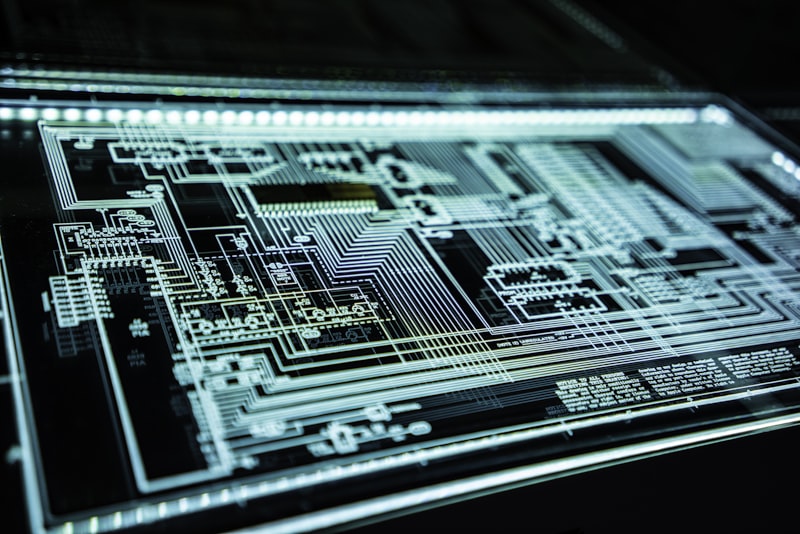
Your ISP Router Is Not a Firewall
The basic modem your internet provider gave you was never designed to protect a business. It has no intrusion prevention, no traffic inspection, and no ability to segment your network. Modern threats demand Next-Generation Firewalls that actively analyze every packet crossing your perimeter.
- Deep Packet Inspection (DPI) to analyze encrypted traffic for hidden malware.
- Intrusion Prevention Systems (IPS) that block known exploits in real time.
- Application control to restrict access to risky or non-business applications.
- Gateway antivirus and anti-spyware scanning at the network edge.
- Geo-IP blocking to automatically drop traffic from high-risk countries.
- SD-WAN integration for multi-site businesses with failover connectivity.
Frequently Asked Questions
Common questions about network security. Contact us if you don't see yours.